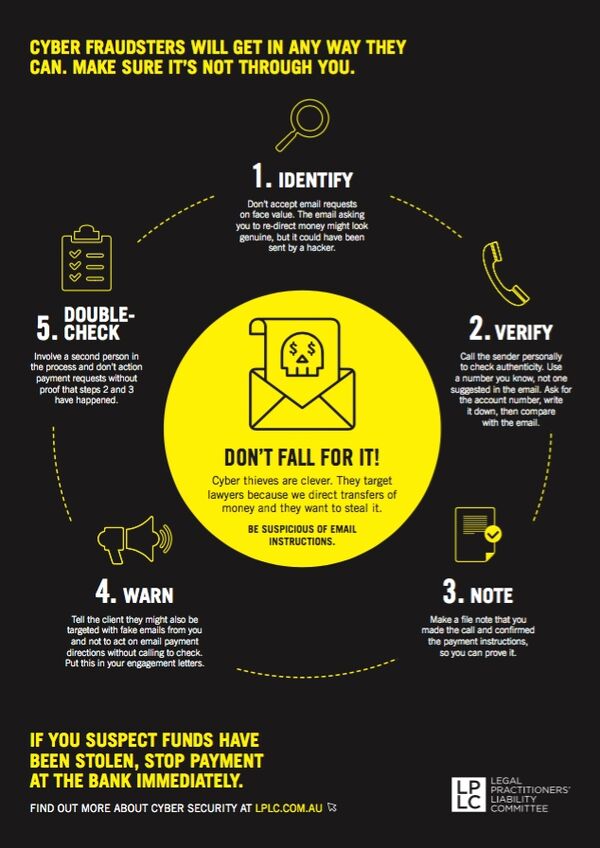
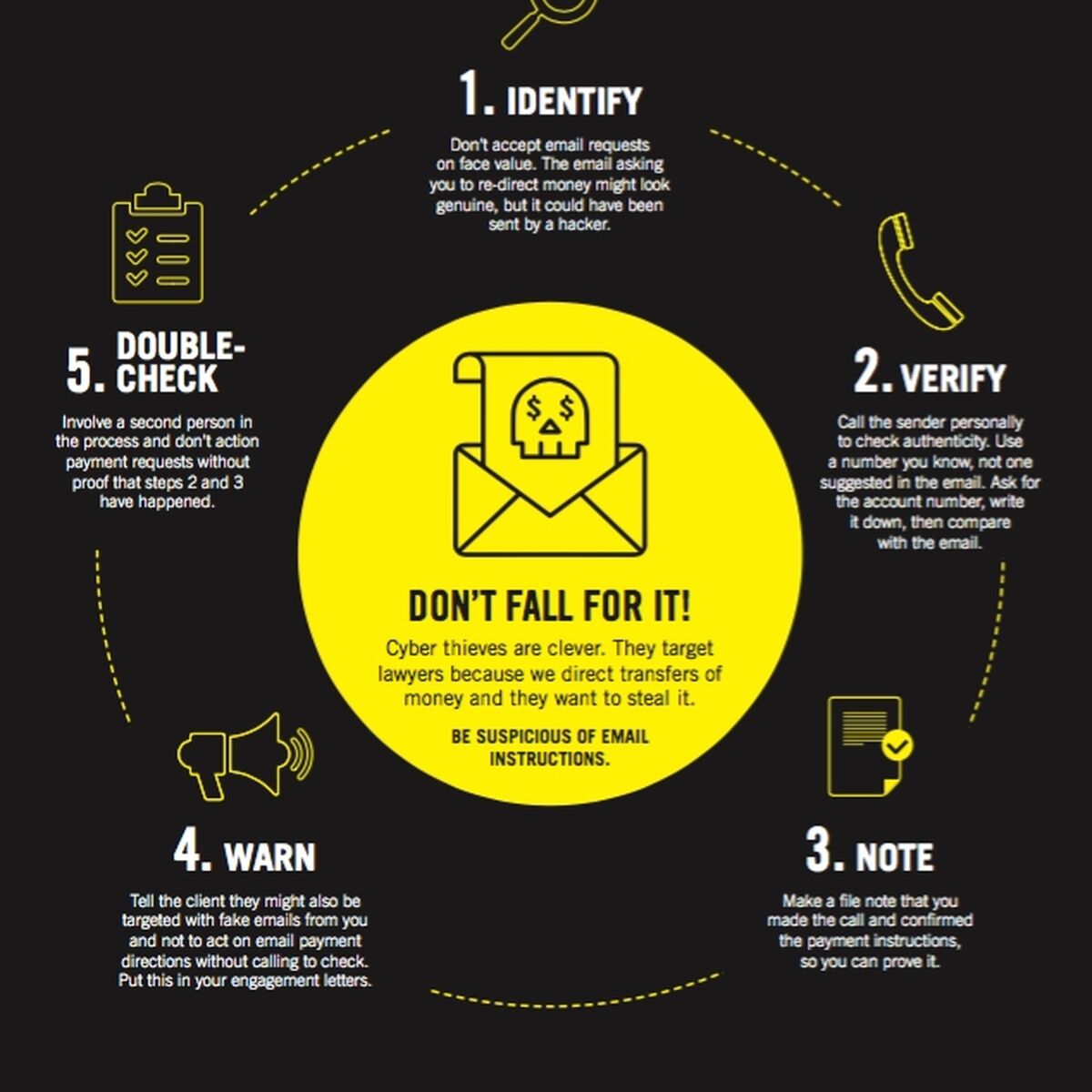
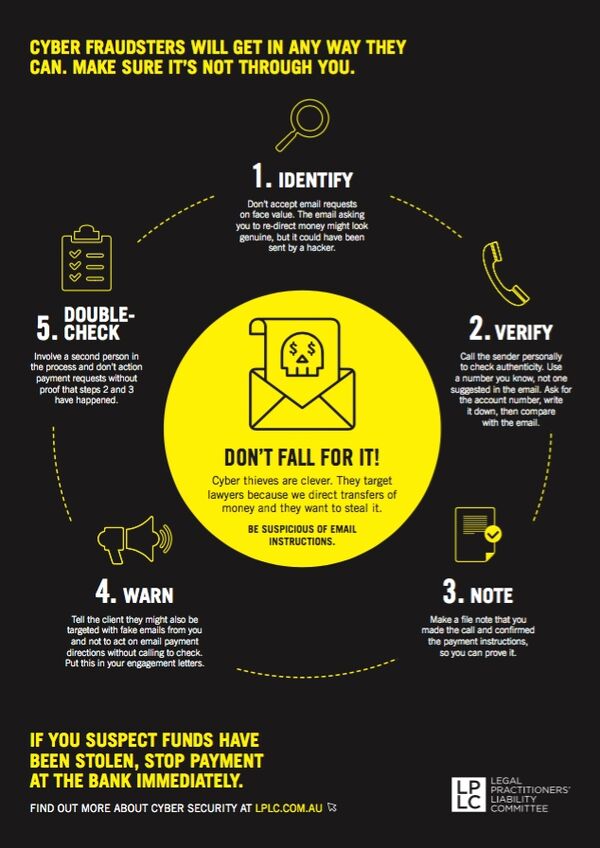
Cyber thieves are clever. They target lawyers because we direct transfers of money and they want to steal it.
Here are 5 steps you can take to protect yourself.
Download and display our handy poster.
- Cyber thieves are clever.
- They target lawyers because we direct transfers of money and they want to steal it.
- Be suspicious of email instructions.
- Cyber fraudsters will get in any way they can.
- Make sure it’s not through you.
5 steps to protect yourself
- Identify – Don’t accept email requests on face value. The email asking you to re-direct money might look genuine, but it could have been sent by a hacker.
- Verify – Call the sender personally to check authenticity. Use a number you know, not one suggested in the email. Ask for the account number, write it down, then compare with the email.
- Note – Make a file note that you made the call and confirmed the payment instructions, so you can prove it.
- Warn – Tell the client they might also be targeted with fake emails from you and not to act on email payment directions without calling to check. Put this in your engagement letters.
- Double-check – Involve a second person in the process and don’t action payment requests without proof that steps 2 and 3 have happened.
If you suspect funds have been stolen, stop payment at the bank immediately.
Download our cyber security poster for your office
A3 Cyber Fraudsters poster1.pdf
Download our 'call before you pay' email signature banner
Transferring money? Use our ‘Call before you pay’ banner in your email signature block and help us increase awareness of cyber-safety.

Call before you pay email footer.png
Open this file via the download button and 'save as' an image to add this email banner to your corporate email signature block.
It can happen to you - here's how
No firm is immune from cyber-criminals and their fake emails. We are seeing an increase in attempts to steal money by hackers masquerading as either the client or the lawyer in fake emails. Below is a summary of two of our recent notifications.
The law firm duped
The firm acted for the vendors of a regional property sold for $295,000 with final settlement due in October.
Shortly before settlement, the firm emailed the client confirming payout details and requesting the client’s bank account details.
The client received the email and responded but the firm did not receive that response. Instead they received an email, purportedly from the client but actually from a hacker, setting out details of the account into which the net settlement proceeds should be paid.
Settlement occurred three days later and $110,000 was paid to the hacker’s bank account a further six days after that.
The following day the client phoned the firm to ask whether the property had settled and when they would receive the proceeds. On realising the earlier ‘email instructions’ were fraudulent, the principal’s secretary swiftly contacted the firm’s paying bank as well as the receiving bank into which the funds had been deposited. Fortunately, most of the money was still in the account and was able to be frozen by the bank and recovered. However, a claim was made against the firm for the small shortfall on the basis of a breach of trust in paying settlement money to an account the client had not authorised.
The client duped
The law firm acted for a purchaser of residential property. Their trust account details were provided in the initial engagement letter.
During the matter the client began receiving emails purporting to be from the firm but which were actually from a hacker. The client was asked to deposit $75,000 into the firm’s trust account and helpfully the email included the bank account details. The client responded to the email querying whether the account details were correct as they were different from the details previously provided. The hacker confirmed the new details to be correct and the funds were transferred to the new account and immediately transferred off shore.
The client had to find an additional $75,000 to settle.